Best Privileged Access Management Software 2026
The best privileged access management software in 2026 is CyberArk Privileged Access Manager because of its advanced credential vaulting, session monitoring, Zero Trust security architecture, and enterprise-grade compliance capabilities. However, BeyondTrust, Delinea, ManageEngine PAM360, and KeeperPAM are also excellent options depending on company size, budget, and infrastructure complexity.
Introduction
Privileged accounts are among the most targeted assets in modern cyberattacks. In 2026, ransomware groups, insider threats, and advanced persistent attackers increasingly focus on administrator credentials because privileged access can unlock an entire organization’s infrastructure within minutes.
According to IBM Security’s Cost of a Data Breach Report, compromised credentials remain one of the leading causes of enterprise breaches globally. Meanwhile, Gartner predicts that by 2027, over 75% of organizations will prioritize identity-first cybersecurity strategies built around Zero Trust access control and privileged identity management.
For businesses in the USA and UK, implementing a robust Privileged Access Management (PAM) solution is no longer optional. Regulatory frameworks including HIPAA, GDPR, SOC 2, PCI DSS, ISO 27001, and NIST increasingly require organizations to monitor, control, and audit privileged account access.
This guide compares the best privileged access management software for 2026, covering features, pricing, compliance support, scalability, deployment complexity, and real-world business use cases to help IT managers and security leaders choose the right PAM platform.
What Is Privileged Access Management (PAM)?
Privileged Access Management (PAM) is a cybersecurity framework and software category designed to secure, monitor, and control privileged accounts within an organization.
Privileged accounts include:
- System administrators
- Domain admins
- Database administrators
- Cloud infrastructure admins
- DevOps engineers
- Third-party contractors
- Service accounts
- Root accounts
PAM software helps organizations prevent unauthorized access to critical systems by enforcing:
- Credential vaulting
- Session monitoring
- Least privilege access
- Just-in-time access
- Multi-factor authentication
- Audit logging
- Password rotation
Why PAM Is Critical for Businesses in 2026
Rising Privileged Credential Attacks
Cybercriminals increasingly target privileged accounts because they provide unrestricted access to:
- Servers
- Cloud infrastructure
- Financial systems
- Customer databases
- Active Directory
- SaaS platforms
According to Verizon’s Data Breach Investigations Report, stolen credentials remain one of the top attack vectors in ransomware incidents.
Key Benefits of PAM Software
| Benefit | Business Impact |
|---|---|
| Credential Protection | Prevents password theft |
| Session Monitoring | Tracks admin activities |
| Compliance Readiness | Supports HIPAA, GDPR, SOC 2 |
| Least Privilege Enforcement | Reduces insider threats |
| Automated Password Rotation | Eliminates static credentials |
| Audit Logging | Improves incident investigations |
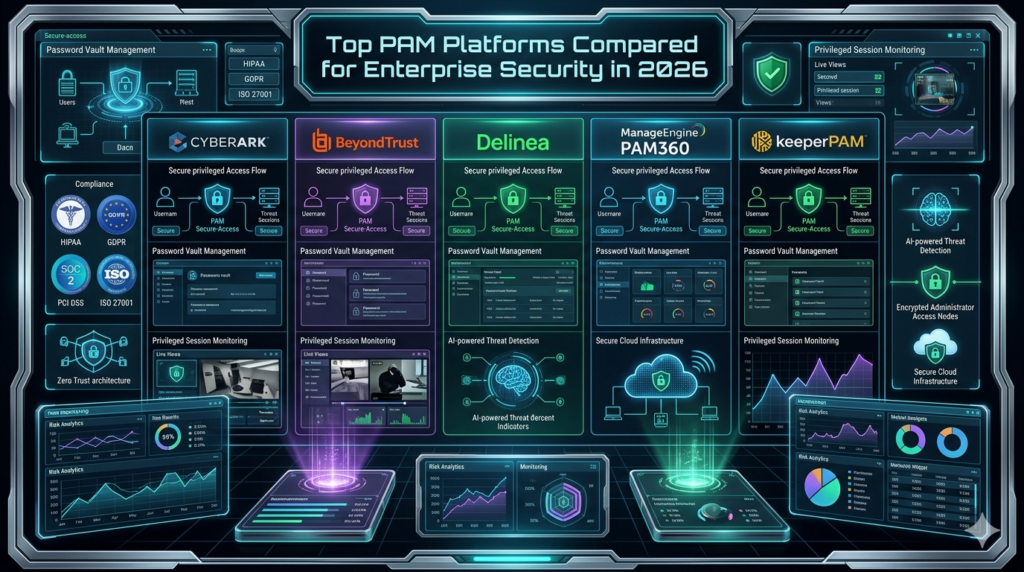
Best Privileged Access Management Software 2026
Feature Comparison Table
| Software | Best For | Deployment | Compliance Support | Starting Price | Rating |
|---|---|---|---|---|---|
| CyberArk | Enterprise security | Cloud & On-Prem | HIPAA, PCI DSS, SOC 2 | Custom | 4.9/5 |
| BeyondTrust | Hybrid infrastructure | Cloud & Hybrid | GDPR, ISO 27001 | Custom | 4.8/5 |
| Delinea | Mid-market businesses | Cloud & On-Prem | SOC 2, HIPAA | Custom | 4.7/5 |
| ManageEngine PAM360 | Budget-conscious SMBs | On-Prem & Cloud | GDPR, PCI DSS | Starts at $595/year | 4.6/5 |
| KeeperPAM | Small businesses | Cloud | SOC 2, GDPR | $2/user/month | 4.5/5 |
| One Identity Safeguard | Large IT environments | Hybrid | NIST, ISO 27001 | Custom | 4.6/5 |
1. CyberArk Privileged Access Manager
Why CyberArk Is the Best PAM Software Overall
CyberArk continues to dominate the PAM market in 2026 due to its enterprise-grade security controls, advanced analytics, and mature privileged identity management ecosystem.
It is widely used in:
- Financial institutions
- Healthcare organizations
- Government agencies
- Enterprise IT environments
Key Features
- Privileged credential vault
- Session isolation and recording
- AI-driven threat analytics
- Just-in-time privileged access
- Secure remote access
- Secrets management
- Cloud privilege security
Best For
- Enterprises
- Regulated industries
- Hybrid infrastructure
- Large IT environments
Pros
- Industry-leading security
- Advanced session monitoring
- Strong compliance support
- Excellent scalability
- Mature Zero Trust architecture
Cons
- Higher pricing
- Complex deployment for smaller teams
2. BeyondTrust
Best PAM Software for Hybrid Infrastructure
BeyondTrust offers an excellent balance between usability and enterprise security.
Its strong remote access management capabilities make it ideal for businesses supporting hybrid and remote workforces.
Key Features
- Password vaulting
- Privileged remote access
- Endpoint privilege management
- Session auditing
- Threat analytics
- Vendor access management
Pros
- Excellent remote admin security
- Strong endpoint controls
- Flexible deployment models
- Good compliance reporting
Cons
- Premium pricing
- Some advanced features require separate modules
Expert Tip
Businesses with remote IT administrators should prioritize PAM platforms with secure privileged remote access and session recording to reduce insider and third-party vendor risks.
3. Delinea
Best PAM Platform for Mid-Sized Businesses
Formerly known as ThycoticCentrify, Delinea focuses on usability and rapid deployment without sacrificing enterprise-level security.
It is especially attractive for growing businesses that need scalable PAM without heavy operational complexity.
Key Features
- Secret Server
- Privilege elevation
- MFA enforcement
- Application control
- Cloud infrastructure support
- Risk analytics
Pros
- Easier deployment
- Strong UI design
- Flexible licensing
- Good SMB scalability
Cons
- Smaller integration ecosystem than CyberArk
- Advanced analytics limited in lower tiers
4. ManageEngine PAM360
Best Budget PAM Software
ManageEngine PAM360 delivers strong privileged access management features at a significantly lower cost than most enterprise PAM vendors.
It is popular among SMBs and mid-sized organizations with limited cybersecurity budgets.
Key Features
- Password vaulting
- SSH key management
- Session recording
- Role-based access control
- SIEM integrations
- Compliance reports
Pros
- Affordable pricing
- Strong feature set
- Easy onboarding
- Good Active Directory integration
Cons
- Interface feels outdated
- Reporting could improve
5. KeeperPAM
Best Cloud-Native PAM for Small Businesses
KeeperPAM combines password management and privileged access security into a streamlined cloud-native platform.
It works well for smaller businesses seeking simplicity and affordability.
Key Features
- Encrypted password vault
- Secure file storage
- Session management
- MFA integration
- Role-based permissions
- Secrets management
Pros
- Very affordable
- Easy cloud deployment
- User-friendly interface
- Good for remote teams
Cons
- Fewer enterprise-level capabilities
- Limited advanced customization
Pricing Comparison Table
| Vendor | Pricing Model | Free Trial | Best Business Size |
|---|---|---|---|
| CyberArk | Custom enterprise pricing | Demo only | Enterprise |
| BeyondTrust | Custom pricing | Demo only | Mid-Market & Enterprise |
| Delinea | Custom pricing | Yes | SMB & Mid-Market |
| ManageEngine PAM360 | Starts at $595/year | Yes | SMB |
| KeeperPAM | Starts at $2/user/month | Yes | Small Business |
| One Identity Safeguard | Custom pricing | Demo only | Enterprise |
Which PAM Solution Is Best for Compliance?
Best Compliance-Focused PAM Vendors
| Compliance Standard | Recommended Vendor |
|---|---|
| HIPAA | CyberArk |
| GDPR | BeyondTrust |
| SOC 2 | Delinea |
| PCI DSS | ManageEngine PAM360 |
| ISO 27001 | One Identity |
| NIST Alignment | CyberArk |
Organizations handling sensitive customer data or financial systems should prioritize vendors with advanced audit trails and privileged session recording.
Also, read Best Single Sign-On Solution for Small Business 2026.
How to Choose the Best Privileged Access Management Software
1. Evaluate Infrastructure Complexity
Choose PAM software that supports:
- On-prem servers
- Hybrid cloud
- Multi-cloud infrastructure
- DevOps environments
- SaaS integrations
2. Prioritize Session Monitoring
Advanced session recording and analytics are critical for:
- Insider threat detection
- Compliance audits
- Incident response
- Forensics investigations
3. Look for Zero Trust Features
Modern PAM solutions should support:
- Least privilege access
- Just-in-time elevation
- Behavioral analytics
- Adaptive authentication
4. Analyze Total Cost of Ownership
Many PAM vendors charge separately for:
- Endpoint privilege management
- Remote access modules
- Secrets management
- Advanced analytics
Always evaluate long-term scalability costs.
Pro Tip
Small businesses often overestimate their PAM requirements. Start with password vaulting and MFA, then expand into full privileged session management as your infrastructure grows.
Real-World Business Example
A mid-sized healthcare provider in Texas implemented BeyondTrust PAM across its remote IT environment after failing a HIPAA audit.
Within six months, the organization achieved:
- Full privileged session logging
- Automated password rotation
- Reduced unauthorized admin activity
- Improved HIPAA compliance reporting
- Faster incident investigations
This demonstrates how PAM platforms directly improve operational security and regulatory readiness.
Common PAM Mistakes Businesses Make
1. Protecting Only Human Accounts
Many organizations forget to secure:
- Service accounts
- API credentials
- DevOps secrets
- SSH keys
Modern PAM strategies must secure machine identities too.
2. Ignoring Third-Party Access
Contractors and vendors frequently receive privileged access without monitoring.
Always enforce:
- MFA
- Session recording
- Time-limited access
3. Overcomplicating Policies
Excessively strict policies can slow IT productivity.
Balance security with operational efficiency.
Frequently Asked Questions (FAQ)
What is the best privileged access management software in 2026?
CyberArk is currently the best overall PAM software due to its advanced security controls, scalability, and compliance capabilities.
Why is PAM important for cybersecurity?
PAM protects privileged accounts that attackers commonly target to gain full access to systems, networks, and sensitive data.
Is PAM only for enterprises?
No. Modern PAM solutions such as KeeperPAM and ManageEngine PAM360 are affordable and suitable for SMBs.
What is the difference between IAM and PAM?
IAM manages general user identities and access, while PAM specifically secures high-level privileged accounts with elevated permissions.
Does PAM support Zero Trust security?
Yes. Most modern PAM platforms support Zero Trust principles including least privilege access and continuous authentication.
Which PAM solution is best for SMBs?
ManageEngine PAM360 and KeeperPAM are excellent choices for SMBs due to affordability and ease of deployment.
Can PAM help with compliance?
Yes. PAM platforms help businesses meet compliance requirements including HIPAA, GDPR, SOC 2, PCI DSS, and ISO 27001.
Final Verdict: Which PAM Solution Wins in 2026?
Winner: CyberArk Privileged Access Manager
After comparing security capabilities, compliance support, scalability, usability, and infrastructure flexibility, CyberArk remains the best privileged access management software in 2026.
Why CyberArk Wins
- Industry-leading PAM security
- Advanced threat analytics
- Excellent session monitoring
- Enterprise-grade compliance support
- Mature Zero Trust architecture
Best Alternatives
- BeyondTrust — Best for hybrid remote access security
- Delinea — Best for mid-market businesses
- ManageEngine PAM360 — Best budget-friendly PAM platform
- KeeperPAM — Best cloud-native SMB solution
Conclusion
Privileged accounts remain one of the most valuable targets for cybercriminals in 2026. Without strong privileged access controls, businesses face increased risks from ransomware, insider threats, credential theft, and regulatory violations.
The best privileged access management software helps organizations:
- Secure administrator credentials
- Enforce Zero Trust access
- Monitor privileged sessions
- Reduce insider threats
- Improve compliance readiness
For most enterprises, CyberArk remains the strongest overall PAM platform. However, SMBs and mid-sized organizations may achieve better ROI with solutions like Delinea, ManageEngine PAM360, or KeeperPAM depending on infrastructure complexity and budget.
Visit LifeSure Security for more cybersecurity software reviews, IAM buying guides, Zero Trust security comparisons, and enterprise cybersecurity insights.
Disclaimer
Software pricing, features, integrations, and compliance capabilities may change over time. Always verify current product details directly from official vendor websites before making purchasing decisions. This article is for informational purposes only and does not constitute legal, compliance, or cybersecurity consulting advice.