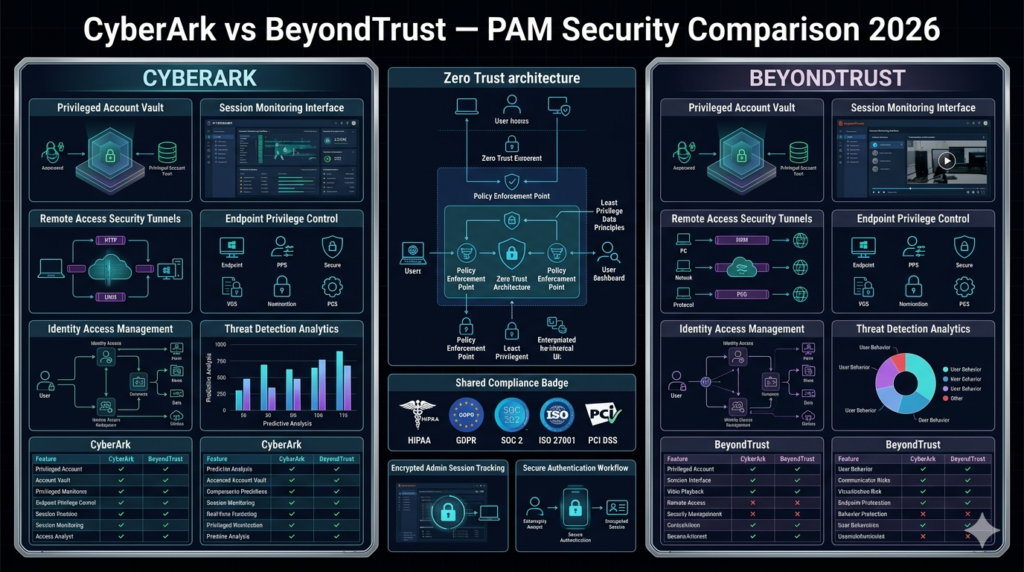
BeyondTrust vs CyberArk PAM Comparison 2026
CyberArk is the overall leader in privileged access management (PAM) due to its deeper security capabilities, advanced threat analytics, and enterprise-grade Zero Trust architecture. However, BeyondTrust is a strong alternative for organizations needing simpler deployment, better remote access controls, and hybrid infrastructure support.
If security depth is the priority → CyberArk wins
If usability and hybrid access are priorities → BeyondTrust wins
Introduction
Privileged Access Management (PAM) is one of the most critical layers of cybersecurity in 2026. With rising ransomware attacks, credential theft, and insider threats, organizations in the USA and UK are increasingly investing in PAM platforms to secure administrative accounts and sensitive infrastructure.
Two of the most dominant enterprise PAM solutions are:
- CyberArk Privileged Access Manager
- BeyondTrust Privileged Remote Access
Both platforms are widely used in financial services, healthcare, government, and large enterprise IT environments.
But they serve slightly different security philosophies.
CyberArk focuses on deep identity security and Zero Trust enforcement, while BeyondTrust emphasizes secure remote access and operational simplicity.
This comparison breaks down everything IT leaders need to know before choosing between them.
What Is CyberArk?
CyberArk Privileged Access Manager is considered the market leader in privileged access security. It is designed to secure, monitor, and control privileged accounts across complex enterprise environments.
Key Features
- Privileged credential vaulting
- Just-in-time access (JIT)
- Session recording and monitoring
- Threat analytics and anomaly detection
- Secrets management for DevOps
- Endpoint privilege security
- Cloud PAM for hybrid environments
Strengths
- Deep enterprise security controls
- Advanced Zero Trust implementation
- Excellent compliance reporting (HIPAA, SOC 2, PCI DSS)
- Strong threat intelligence integration
Weaknesses
- Expensive licensing
- Complex deployment
- Requires skilled security teams
What Is BeyondTrust?
BeyondTrust Privileged Remote Access is a PAM platform designed for secure remote access, endpoint privilege management, and credential protection.
It is widely used by IT operations teams that need strong security without excessive complexity.
Key Features
- Privileged remote access
- Password vaulting
- Endpoint privilege management
- Session monitoring and recording
- Vendor access control
- Least privilege enforcement
Strengths
- Easier to deploy than CyberArk
- Strong remote access security
- Good hybrid IT support
- User-friendly interface
Weaknesses
- Less advanced threat analytics
- Smaller security ecosystem
- Fewer DevOps integrations
CyberArk vs BeyondTrust — Feature Comparison
| Feature | CyberArk | BeyondTrust |
|---|---|---|
| Privileged Credential Vault | Advanced | Strong |
| Session Recording | Enterprise-grade | Strong |
| Zero Trust Support | Very Advanced | Moderate |
| Remote Access Security | Strong | Excellent |
| Threat Analytics | AI-driven | Basic analytics |
| DevOps Secrets Management | Yes | Limited |
| Deployment Complexity | High | Medium |
| Ease of Use | Moderate | High |
Security Comparison (Critical Factor)
CyberArk Security Advantage
CyberArk leads in:
- Behavioral anomaly detection
- AI-driven risk scoring
- Privileged identity segmentation
- Just-in-time access control
- Deep integration with SIEM tools
It is designed for organizations where breach prevention is more important than convenience.
BeyondTrust Security Approach
BeyondTrust focuses on:
- Secure remote access tunnels
- Endpoint privilege control
- Session isolation
- Vendor access security
It is more operationally focused than deeply analytical.
Pricing Comparison
| Platform | Pricing Model | Estimated Cost | Best Fit |
|---|---|---|---|
| CyberArk | Enterprise custom pricing | $$$$ | Large enterprises |
| BeyondTrust | Custom pricing | $$$ | Mid-to-large enterprises |
💡 Neither tool is budget-friendly, but CyberArk is typically more expensive due to its advanced security stack.
Compliance Support
Both platforms support major compliance frameworks:
- HIPAA (Healthcare US)
- GDPR (UK/EU)
- SOC 2 Type II
- PCI DSS
- ISO 27001
- NIST Cybersecurity Framework
Winner for Compliance:
👉 CyberArk (slightly stronger audit and reporting depth)
Ease of Deployment
CyberArk
- Complex architecture
- Requires trained security engineers
- Longer implementation cycle
BeyondTrust
- Faster deployment
- Easier onboarding
- Less operational overhead
Winner:
👉 BeyondTrust (for simplicity)
Also read Best Privileged Access Management Software 2026.
Real-World Use Cases
CyberArk Use Case
A global banking institution uses CyberArk to:
- Secure 10,000+ privileged accounts
- Monitor admin sessions across global data centers
- Enforce Zero Trust policies across hybrid cloud
- Detect insider threats in real time
BeyondTrust Use Case
A healthcare IT provider uses BeyondTrust to:
- Secure remote access for 300+ IT contractors
- Monitor vendor sessions
- Control endpoint privilege escalation
- Simplify IT support workflows
Pros and Cons Summary
CyberArk Pros
- Industry-leading PAM security
- Advanced Zero Trust architecture
- Best-in-class threat detection
- Strong compliance reporting
CyberArk Cons
- Expensive
- Complex deployment
- Requires specialized expertise
BeyondTrust Pros
- Easier to deploy and manage
- Excellent remote access security
- Strong endpoint privilege control
- Better usability for IT teams
BeyondTrust Cons
- Less advanced AI security
- Smaller ecosystem than CyberArk
- Limited DevOps features
Expert Insight (Important)
In real-world enterprise security environments, PAM tools are not just software—they are risk governance systems.
CyberArk is built for:
“Preventing sophisticated attacks before they happen”
BeyondTrust is built for:
“Securely managing access with operational efficiency”
This difference defines their entire architecture.
Which One Should You Choose?
Choose CyberArk if:
- You are a large enterprise
- You need advanced Zero Trust security
- You operate in regulated industries
- You require deep threat analytics
- Security is your top priority
Choose BeyondTrust if:
- You want faster deployment
- You manage hybrid IT environments
- You rely heavily on remote access
- You want easier administration
- You prefer usability over complexity
Final Verdict
🏆 Winner: CyberArk
In a direct BeyondTrust vs CyberArk comparison, CyberArk wins overall due to:
- Superior security architecture
- Advanced threat intelligence
- Stronger Zero Trust implementation
- Better compliance depth
However, BeyondTrust remains a highly competitive and more user-friendly alternative, especially for organizations that prioritize operational simplicity.
Conclusion
Choosing the right PAM platform in 2026 depends on your organization’s security maturity, infrastructure complexity, and compliance requirements.
If your priority is maximum security and enterprise-grade protection, CyberArk is the clear leader. If your priority is ease of use and secure remote operations, BeyondTrust is a strong choice.
Both platforms significantly improve privileged access security compared to traditional IAM systems and are essential for modern Zero Trust architectures.
For more cybersecurity software comparisons, PAM guides, and enterprise security reviews, visit lifesure.site.
Disclaimer
This article is for informational purposes only. Pricing, features, and product capabilities may change over time. Always verify details from official vendor sources before making purchasing decisions.